On October 15th, the Cybersecurity and Infrastructure Security Agency (CISA) issued a directive to address critical vulnerabilities in F5 devices. While they note an immediate risk to Federal networks, the risk and their mitigation recommendations are much broader. As CISA’s Acting Director, Madhu Gottumukkala, states, “These same risks extend to any organization using this technology, potentially leading to catastrophic compromise of critical information systems.” Credential and IP theft are among the risks of this sophisticated supply chain attack, with immediate remediation recommended by both CISA and the UK’s National Cyber Security Center.
Background
F5 is a technology and cybersecurity company that provides cloud and application security, and thus is relied on by its customers for their own cybersecurity. On Wednesday, F5 issued an SEC regulatory filing disclosing the breach, and customers received a threat hunting guide to identify Brickstorm, a malware used by Chinese state-backed threat groups. Brickstorm malware is a backdoor that enables malicious actors persistent access to an organization. The attackers associated with Brickstorm often use the malware for espionage and source code theft, which is then analyzed for software bugs. Once those software bugs are identified, they are, in turn, exploited to breach the customers of that software. This dual-purpose attack makes this an especially concerning breach and is illustrative of the growing complexity and impact of digital supply chain attacks. The SEC filing also notes the DOJ permitted a delay to their disclosure based on a substantial risk to national security or public safety.
Network Effects
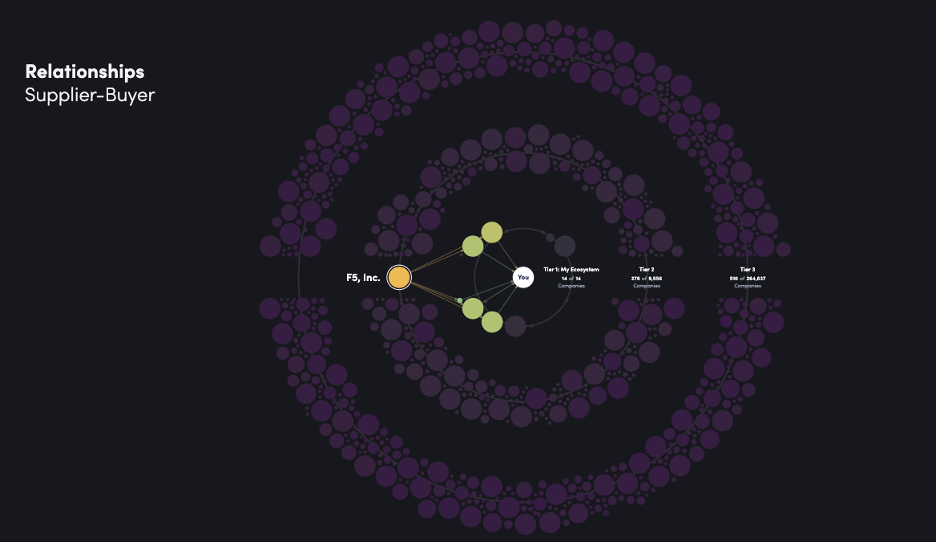
A global scan of F5 BIG-IP instances surfaces over 266,000 potentially vulnerable devices, largely located in the U.S. In a recent blog, F5 notes that they support over 23,000 customers across 170 countries. However, these direct customer relationships do not reflect the entire scope and potential exposure in supply chain attacks. Instead, when assessing potential supply chain attack situations, it is useful to explore a broader impact based on extended supplier-buyer relationships, especially in attacks that exhibit such persistent, long-term access.
Analyzing interos.ai’s buyer-supplier relationship graph and assessing the potential risks across F5’s tiers 1 through 3 buyer-supplier relationships, over 3.7 M companies have direct or indirect (e.g., third-party risk) connections across these tiers. The top industries represented across these connections are: software and technology, business management and legal services, banking and financial services, architectural, engineering and design services, construction, and consumer goods. In addition, while these companies have the largest footprint in the United States, across the extended tiers, the United Kingdom, India, China, Germany and Canada have expansive connections.
The Urgency to Mitigate
F5 learned of the breach in August but notes that the “nation-state threat actor maintained long-term, persistent access to, and downloaded files from, certain F5 systems.” While they claim to have contained the breach, CISA identifies this as a significant risk due to the persistent, long-term access to F5 systems, and specifically BIG-IP. Importantly, they claim there is no evidence of access to, or exfiltration of, data or any modification of their software supply chain, but given the persistent nature of the threat actors presence, and because certain files containing BIG-IP source code were downloaded, the recommendation remains to immediately update and install the patches.
As we’ve seen time and time again (from Jaguar Land Rover to Discord recently), third-party data breaches remain on the rise, comprising anywhere between 30% and 60% of breaches over the last year. This is only CISA’s third directive released this year, which is illustrative of the urgency to update and patch any relevant systems. CISA recommends adhering to F5’s recommended updates immediately. They detail the affected products, as well as over two dozen high severity CVEs along with additional medium and low severity CVEs, and mitigation steps. We will continue to monitor this and report any updates to this dynamic situation.
Learn how interos.ai can help your organization detect, map, and mitigate supply chain risk in real time.